Azure AD
Support level: Community
Preparation
The following placeholders are used in this guide:
authentik.companyis the FQDN of the authentik install.
Azure setup
-
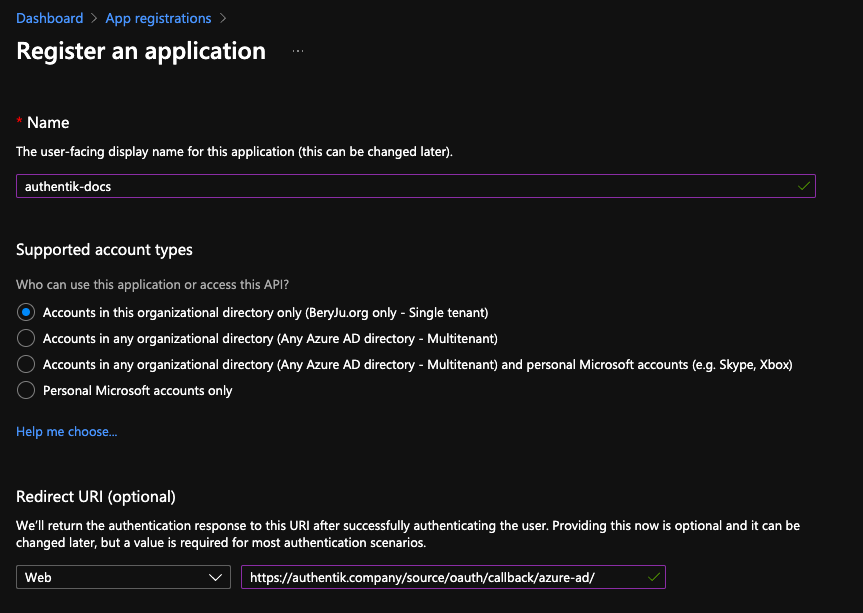
Navigate to portal.azure.com, and open the App registration service
-
Register a new application
Under Supported account types, select whichever account type applies to your use-case.
-
Take note of the Application (client) ID value.
If you selected Single tenant in the Supported account types prompt, also note the Directory (tenant) ID value.
-
Navigate to Certificates & secrets in the sidebar, and to the Client secrets tab.
-
Add a new secret, with an identifier of your choice, and select any expiration. Currently the secret in authentik has to be rotated manually or via API, so it is recommended to choose at least 12 months.
-
Note the secret's value in the Value column.
authentik Setup
In authentik, create a new Azure AD OAuth Source in Resources -> Sources.
Use the following settings:
- Name:
Azure AD - Slug:
azure-ad(this must match the URL being used above) - Consumer key:
*Application (client) ID* value from above - Consumer secret:
*Value* of the secret from above
If you kept the default Supported account types selection of Single tenant, then you must change the URL below as well:
- OIDC Well-known URL:
https://login.microsoftonline.com/*Directory (tenant) ID* from above/v2.0/.well-known/openid-configuration

Save, and you now have Azure AD as a source.
For more details on how-to have the new source display on the Login Page see here.
Automatic user enrollment and attribute mapping
Using the following process you can auto-enroll your users without interaction, and directly control the mapping Azure attribute to authentik. attribute.
- Create a new Expression Policy (see here for details).
- Use azure-ad-mapping as the name.
- Add the following code and adjust to your needs.
# save existing prompt data
current_prompt_data = context.get('prompt_data', {})
# make sure we are used in an oauth flow
if 'oauth_userinfo' not in context:
ak_logger.warning(f"Missing expected oauth_userinfo in context. Context{context}")
return False
oauth_data = context['oauth_userinfo']
# map fields directly to user left hand are the field names provided by
# the microsoft graph api on the right the user field names as used by authentik
required_fields_map = {
'name': 'username',
'upn': 'email',
'given_name': 'name'
}
missing_fields = set(required_fields_map.keys()) - set(oauth_data.keys())
if missing_fields:
ak_logger.warning(f"Missing expected fields. Missing fields {missing_fields}.")
return False
for oauth_field, user_field in required_fields_map.items():
current_prompt_data[user_field] = oauth_data[oauth_field]
# Define fields that should be mapped as extra user attributes
attributes_map = {
'upn': 'upn',
'family_name': 'sn',
'name': 'name'
}
missing_attributes = set(attributes_map.keys()) - set(oauth_data.keys())
if missing_attributes:
ak_logger.warning(f"Missing attributes: {missing_attributes}.")
return False
# again make sure not to overwrite existing data
current_attributes = current_prompt_data.get('attributes', {})
for oauth_field, user_field in attributes_map.items():
current_attributes[user_field] = oauth_data[oauth_field]
current_prompt_data['attributes'] = current_attributes
context['prompt_data'] = current_prompt_data
return True
- Create a new enrollment flow azure-ad-enrollment (see here for details).
- Add the policy default-source-enrollment-if-sso to the flow. To do so open the newly created flow. Click on the tab Policy/Group/User Bindings. Click on Bind existing policy and choose default-source-enrollment-if-sso from the list.
- Bind the stages default-source-enrollment-write (order 0) and default-source-enrollment-login (order 10) to the flow.
- Bind the policy azure-ad-mapping to the stage default-source-enrollment-write. To do so open the flow azure-ad-enrollment open the tab Stage Bindings, open the dropdown menu for the stage default-source-enrollment-write and click on Bind existing policy Select azure-ad-mapping.
- Open the source azure-ad. Click on edit.
- Open Flow settings and choose azure-ad-enrollment as enrollment flow.
Try to login with a new user. You should see no prompts and the user should have the correct information.
Machine-to-machine authenticationauthentik: 2024.12.0+
If using Machine-to-Machine authentication, some specific steps need to be considered.
When getting the JWT token from Azure AD, set the scope to the Application ID URI, and not the Graph URL; otherwise the JWT will be in an invalid format.
POST /<azure-ad-tenant-id>/oauth2/v2.0/token/ HTTP/1.1
Host: login.microsoftonline.com
Content-Type: application/x-www-form-urlencoded
grant_type=client_credentials&
client_id=<application_client_id>&
scope=api://<application_client_id>/.default&
client_secret=<application_client_secret>
The JWT returned from the request above can be used with authentik to exchange it for an authentik JWT.
For instructions on how to display the new source on the authentik login page, refer to the Add sources to default login page documentation.